By David Gascón, CTO of Libelium.
Security in the IoT is one the main concerns for municipalities as Smart Cities projects start being a reality. In the next article we will expose what is the security proposal developed by Libelium for its sensor devices and gateways: Waspmote, ¡Plug & Sense! y Meshlium
In the current article we get into the four main features of Security:
- Privacidad: ensure that only the desired sensor devices and gateways are part of the network
- Authenticity: ensure that the supposed sender is the real sender
- Confidentiality: ensure that the data is only readable by the proposed destination
- Integrity: ensure that the information contained in the original message is kept intact

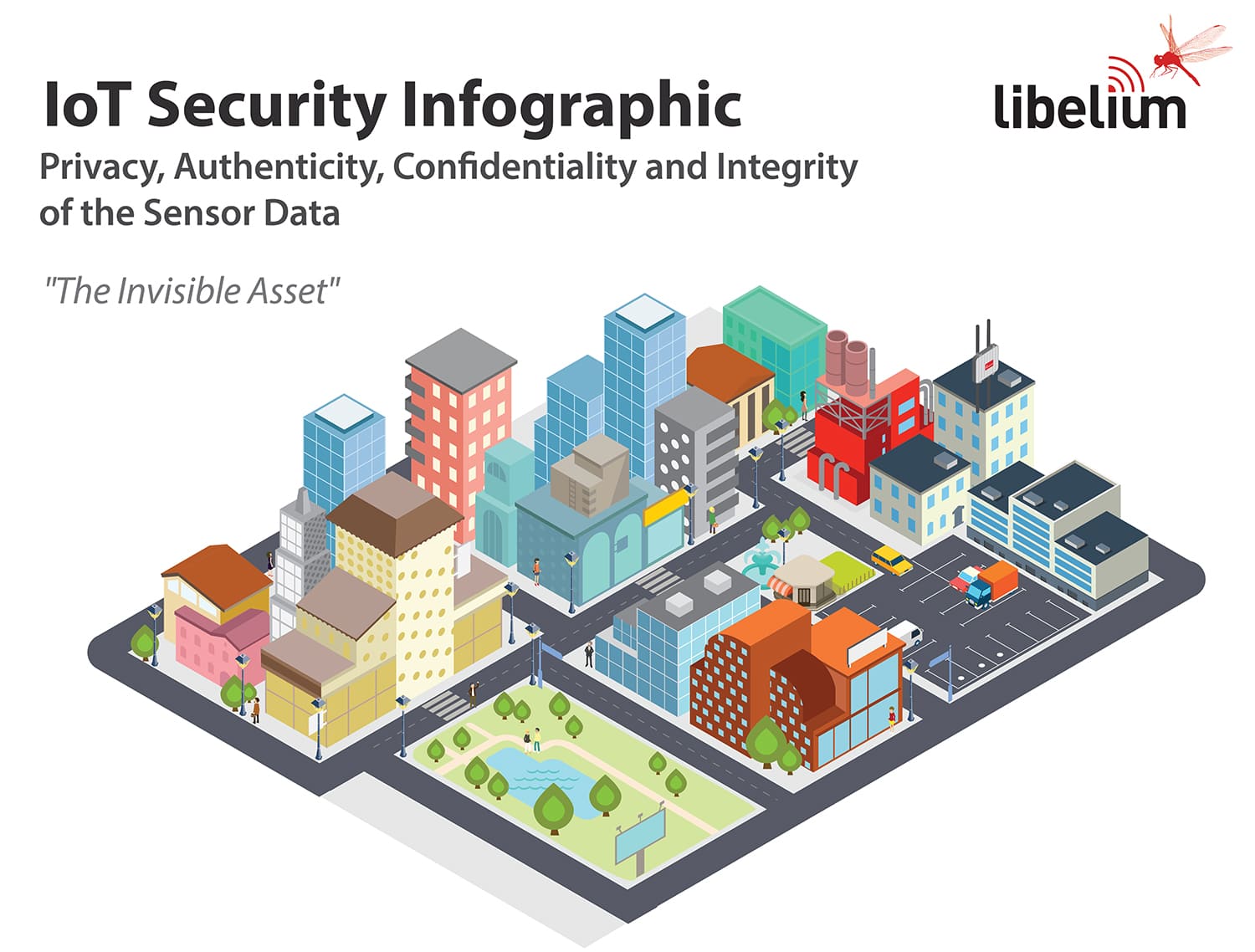
Device to Device (Symmetric Encryption) [Encryption Level 1 – E1]
The end nodes implement a first encryption level at the link layer. All the nodes belonging to the same network share a common pre-shared key. This avoid external devices joining the sensor network (ensuring privacy) or watching the information contained in the packets being sent as it is encrypted (ensuring confidentiality). This encryption process is driven in Waspmote y ¡Plug & Sense! by special electronic hardware included in the radio modules. AES 128b is the most used algorithm in this first layer.

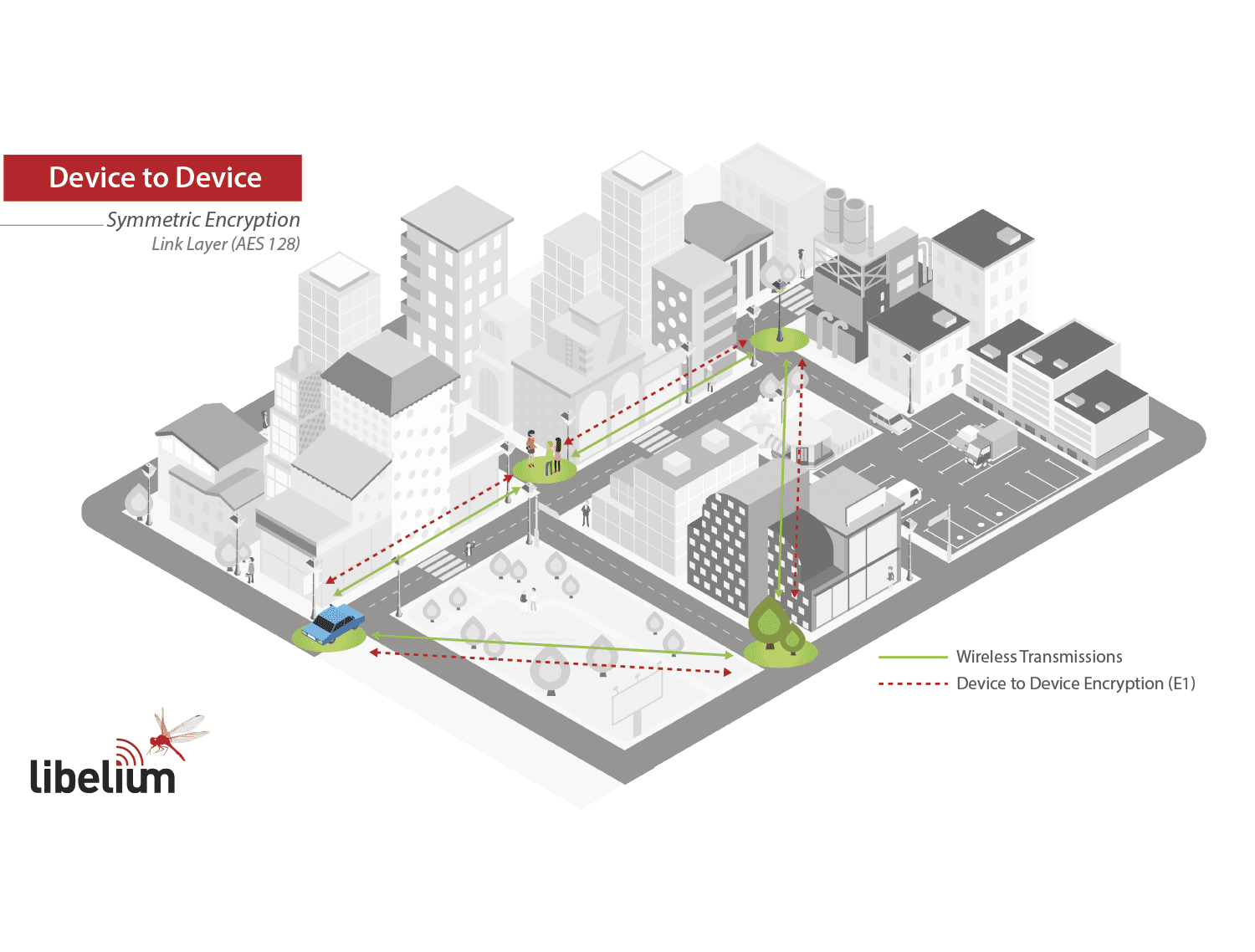
Device to Gateway (Symmetric Encryption) [Encryption Level 2 – E2]
In a Smart City there are many different sensor networks working at the same time, for example we may find the Smart Parking nodes sending data in parallel to the Smart Environment or the Smart Water sensor devices. As all them may share the same E1 key used in the link layer, a new security mechanism is added, this time by using symmetric encryption in the Networking / Application layer – E2.
Now every single node in the network has its own private key (ensuring authenticity) and the Gateway (Meshlium) contains every single key of the devices to be able to decrypt the packets sent. The information goes encrypted from each node to the Gateway so the intermediate nodes can not access to it (ensuring privacy and confidentiality). Adding a sequence number + random internal seed we can perform the checksum to ensure that the data contained has not been altered (ensuring integrity).
The encryption process in Waspmote y ¡Plug & Sense! is driven by software libraries included in the API and run by the MCU. AES 256b is the most used algorithm. Normally it is used in combination with E1 security layer so we get a E1 + E2 security scheme.

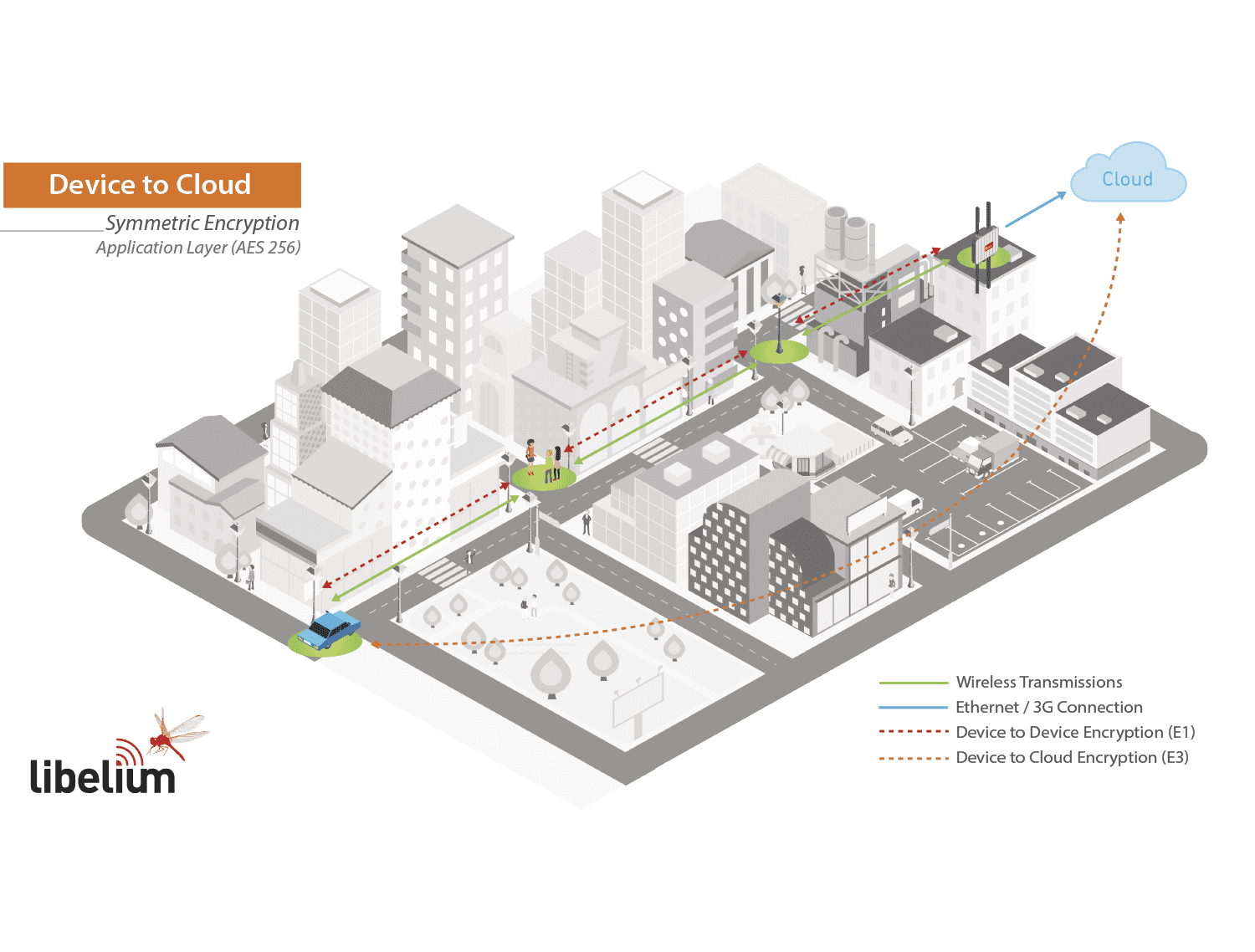
Device to Cloud (Symmetric Encryption) [Encryption Level 3 – E3]
This is similar to E2 but instead of having the keys located in the Gateway they are stored in the Nube. This allows to use different Gateways (trusted or not trusted) as the information goes encrypted through them.
The encryption process is normally driven by software libraries run by the MCU. AES 256b is the most used algorithm. Normally it is used in combination with E1 so we get a E1 + E3 security scheme. The information goes encrypted from each node to the Gateway so the intermediate nodes or the Gateways can not access to it.
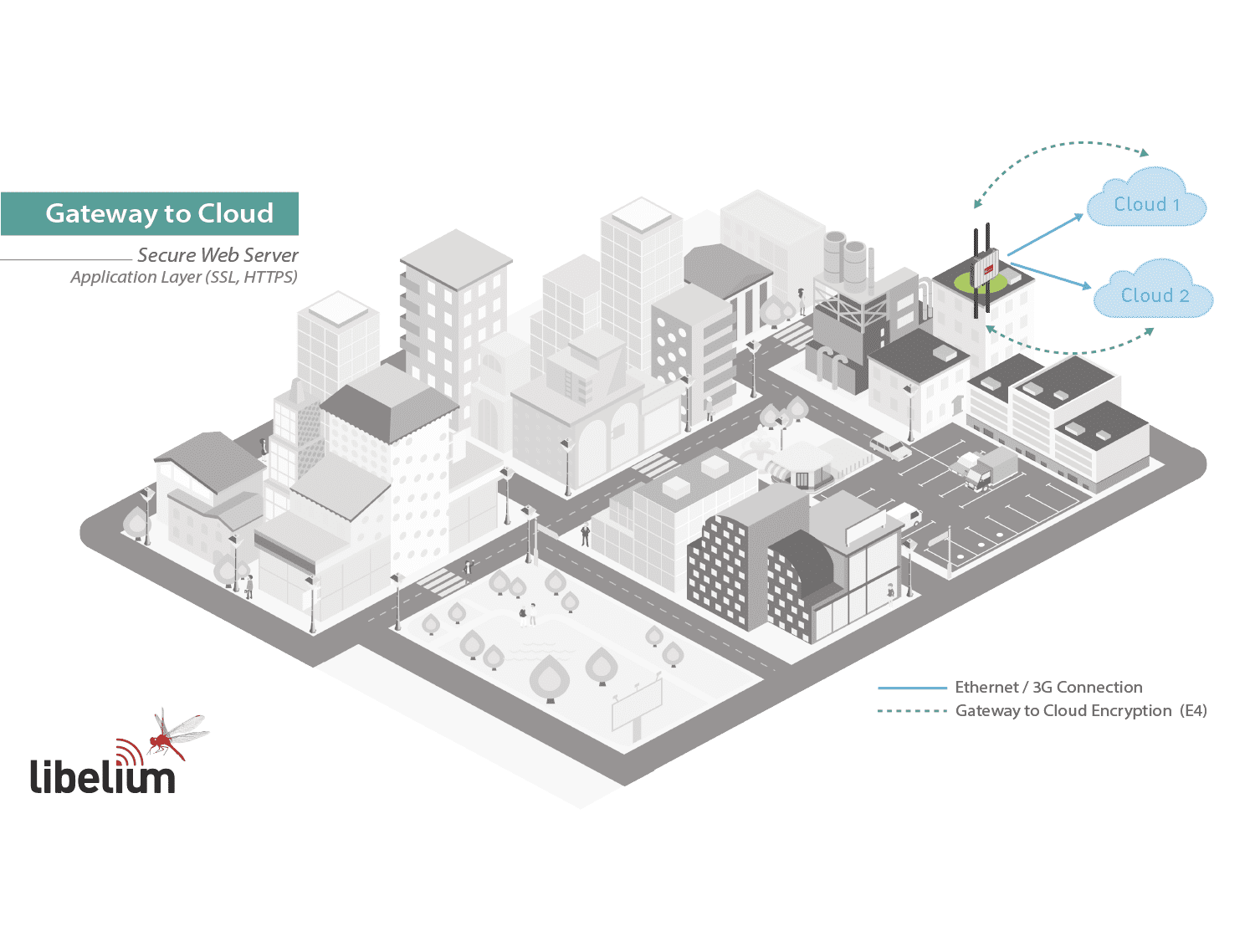
Gateway to Cloud (Secure Web Server – SSL-HTTPS-SSH) [Encryption Level 4 – E4]
La Gateway (Meshlium) use SSL certificates to send the information to the different Cloud Servers. It is the same security scheme as we use with our browsers when we connect to our bank website.
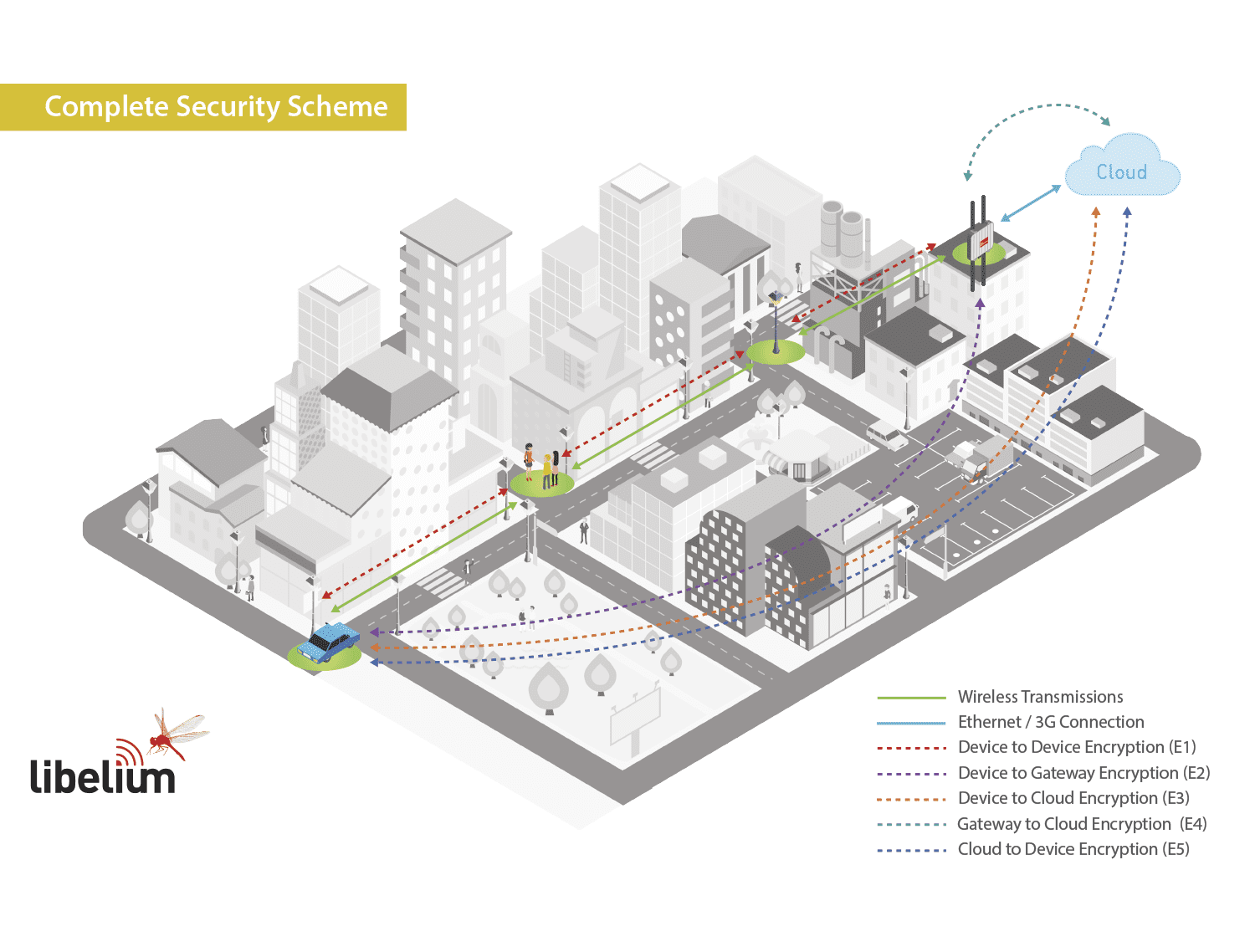
Most common combination scenarios:
- E1 + E2 + E4
- E1 + E3 + E4
The most secure scenario would be the one using combination of all of them: E1 + E2 + E3 + E4 although it would reduce the payload (we would be sending less bytes of information per packet).

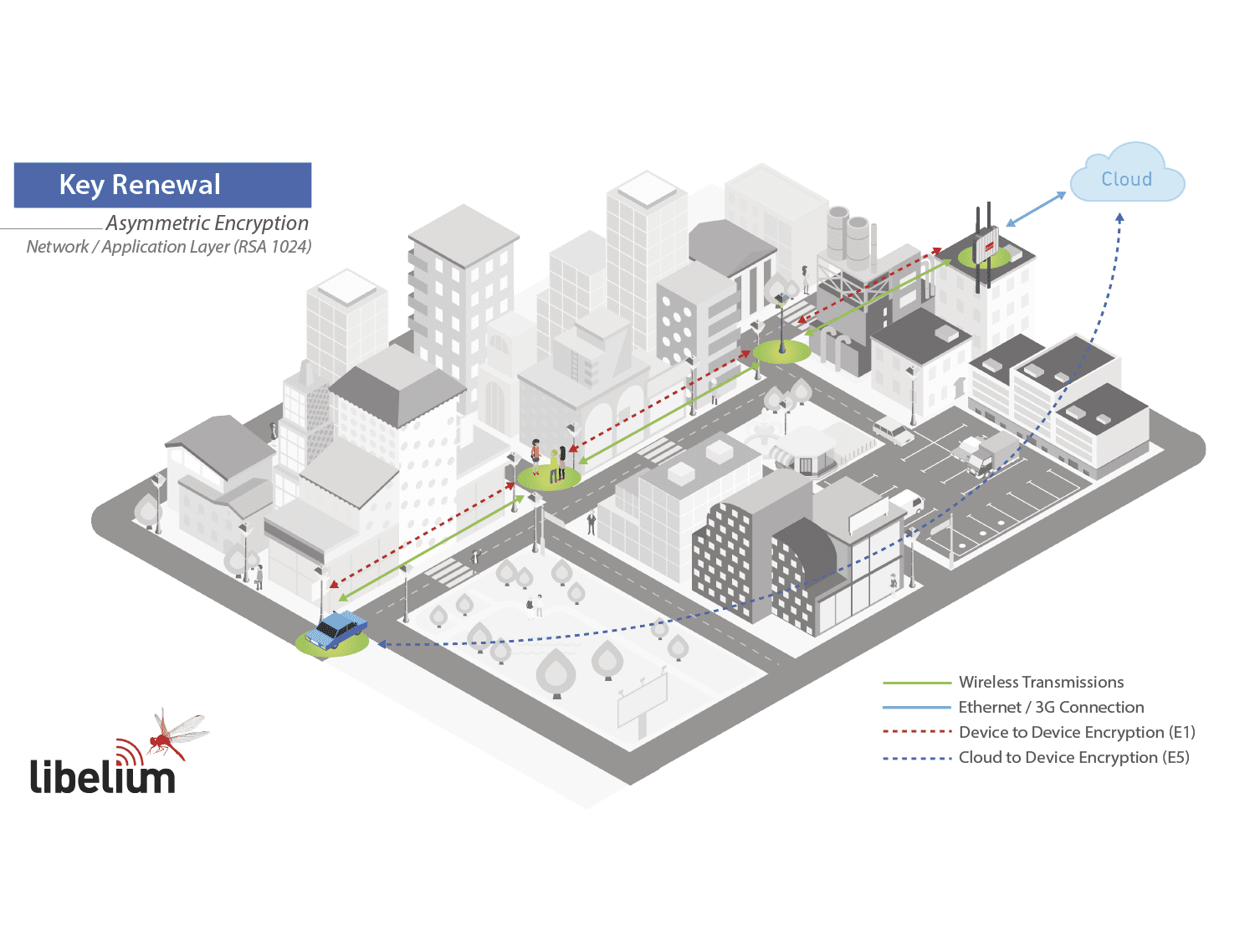
Key Renewal (Asymmetric Encryption) [Encryption Level 5 – E5]
Prior to start with the software encryption with AES 256 we need to share a key between each node (origin) and the Pasarela o el Cloud Server (destination). To do so we can encrypt the new key using RSA 1024 using both Public/Private keys. This way, we ensure authentication, confidentiality and message integrity (as we add also a seed along with the key to generate randomness in the packet transmission). Once we get the shared key we will use it to start encrypting the sensor information as seen in the previous diagram as AES it ensures the maximum performance and and minimum message overload.
The same process is done when we want to renew the AES key.
Common security issues solved with these 5 Encryption Levels:
- Access Control (Privacy)
By using AES 128 in the link layer we ensure that only nodes with the shared key can access to the routing capabilities of the sensor network. If a strange node sends a message to the network the message will be discharged in the first hop so no extra communication resources will be used. The AES 128 algorithm is implemented in the same radio using specific hardware, for this reason the information will be automatically discarded and not even send to the microcontroller. This provides an extra layer of security as the main control unit of the node will not be interrupted from performing basic tasks or event not awaken from the sleep mode (what ensures optimum energy usage). - Authentication
By using its own private keys (AES / RSA) each node ensures the authenticity of the of origin. The Gateway or the Cloud may store all the public and shared keys of the devices so that they can check the packet has been sent by the supposed origin. - Confidencialidad de los datos
By doubling encryption of the messages we ensure that first that only the nodes which form part of the network can see the general routing packets (AES 128 in the link layer) and after that we establish an encryption tunnel by direct P2P encryption between origin and destination (using AES 256). - Integridad de los datos
The new library uses hash algorithms such as MD5 and SHA to create the checksum of the message and to ensure that the final information received correspond with the original sent. - Data Freshness (avoiding packet injection)
Each packet has an exclusive seed which protects the gateway from receiving several identical packets which could be injected from a third party. - Non-repudation
By signing the messages with RSA keys we have also the legal proof that the information sent really was sent by an specific sensor node and not by other. Important in the future when all the sensitive sensor information has to be legally approved.
Por qué los nodos sensores Libelium son inmunes a los ataques de las pasarelas IoT
La security of its IoT devices is the greatest commitment of Libelium. As IBM X-Force announced last week that there were some vulnerabilities in the Meshlium IoT Gateway, new actions were taken immediately by our R&D team offering a new software version released on August 1st.
La plataforma de sensores Libelium se creó inicialmente como una plataforma de desarrollo de código abierto lista para ser utilizada por investigadores y desarrolladores para tener un control total sobre los nodos sensores y las pasarelas IoT. Así es como hace seis años la plataforma de sensores Libelium se convirtió en una solución del mercado IoT mundial.
Desde el principio, nos centramos en ofrecer a los desarrolladores las herramientas adecuadas (API + SDK) para que pudieran tener un control total en cualquier aspecto de la configuración y el rendimiento. En cuanto a la seguridad de los datos recogidos y transmitidos nuestros dispositivos ofrecen la posibilidad de crear hasta 5 niveles de encriptación como se publica en el artículo titulado Infografía de Seguridad IoT - Privacidad, Autenticidad, Confidencialidad e Integridad de los Datos de los Sensores. "El activo invisible". Estos niveles están compuestos por técnicas de cifrado simétrico que utilizan la técnica de cifrado AES 256 en las capas de enlace, red y aplicación, y la RSA 1024 en la capa de aplicación.
Cuando los desarrolladores establecen correctamente estas técnicas de cifrado, pueden conseguir las cuatro características principales de seguridad para sus proyectos IoT: Privacidad para garantizar que sólo formen parte de la red los dispositivos sensores y pasarelas deseados; Autenticidad para garantizar que el supuesto remitente es el remitente real; Confidencialidad garantizar que los datos sólo puedan ser leídos por el destino propuesto; y Integridad para asegurarse de que la información contenida en el mensaje original permanece intacta.
Para garantizar todas estas características los nodos deben estar correctamente configurados, sin embargo parece que IBM no aplicó la configuración correcta para su demo en la Conferencia Black Hat 2018. En estas pruebas los investigadores no aplicaron el cifrado simétrico entre el nodo y la plataforma Cloud utilizando la técnica AES 256. Este cifrado, junto con un paquete firmado y sembrado (RSA 1024), asegura que la información no podría ser corrompida o cambiada, ya que los atacantes no pueden abrir el paquete y acceder a la info, porque las claves se almacenan en cada nodo y en el servidor Cloud, no en el Meshlium IoT Gateway. En este sentido, los posibles piratas informáticos ni siquiera podrían realizar un ataque de "hombre en el medio", ya que los paquetes están firmados y tienen varios contadores internos para garantizar que no se realicen retransmisiones de fuentes no válidas.
Utilizar en esa demo un esquema básico de configuración de los nodos sensores en lugar de aplicar las capas de cifrado completas, proporcionadas por Libelium, muestra un entorno poco fiable, muy alejado de los desarrollos de casos reales. Esta situación puede llevar a pensar que este sencillo esquema de configuración fue creado para hacer fácilmente algunas suposiciones sobre fugas de seguridad en la información de los nodos sensores cuando simplemente no existen cuando se realiza la configuración correcta.
En conclusión, cuando las opciones de seguridad están bien configuradas, aunque la transmisión de la red o la pasarela IoT se vean comprometidas, los datos seguirán estando seguros y no será posible corromperlos ni modificarlos. Lo más importante no es solo disponer de las herramientas adecuadas, sino también saber configurarlas y utilizarlas correctamente.
Para saber más sobre las librerías de encriptación implementadas por Libelium vaya a:
https://www.libelium.com/products/waspmote/encryption
Para obtener más información sobre las características de seguridad de la plataforma Libelium, visite:
https://www.libelium.com/iot-security-infographic-privacy-authenticity-confidentiality-and-integrity-of-the-sensor-data-the-invisible-asset/
For more information about our products go to:
– Gateway (Meshlium): https://www.libelium.com/products/meshlium/
– Waspmote: https://www.libelium.com/products/waspmote/
– Plug & Sense!: https://www.libelium.com/products/plug-sense/
Or ask our Sales Team at:
https://www.libelium.com/contact/
Author: David Gascón, CTO of Libelium.